Enterprise DNS is more than a service layer for name resolution, it is a strategic control plane that underpins security, reliability, and compliance for modern organizations. A failure in DNS can cascade into outages, misrouting, or unverified data delivery, with real business impact across customers, partners, and internal systems. As organizations migrate toward cloud-native and multi-cloud footprints, the demand for an enterprise-grade DNS architecture grows: authoritative DNS that is correctly delegated, secure DNS that defends against manipulation (DNSSEC), and resilient delivery enabled by Anycast networks and cloud-native DNS services. This article offers a practical framework to design, implement, and operate such a DNS stack without resorting to generic, one-size-fits-all solutions. The guidance draws on industry best practices from leading cloud providers and DNS operators. Google Cloud’s DNS best practices emphasize multi-provider resilience and active-active configurations for high availability in cloud-native environments, which is especially relevant to complex enterprise networks. (cloud.google.com)
Foundations of an enterprise DNS architecture
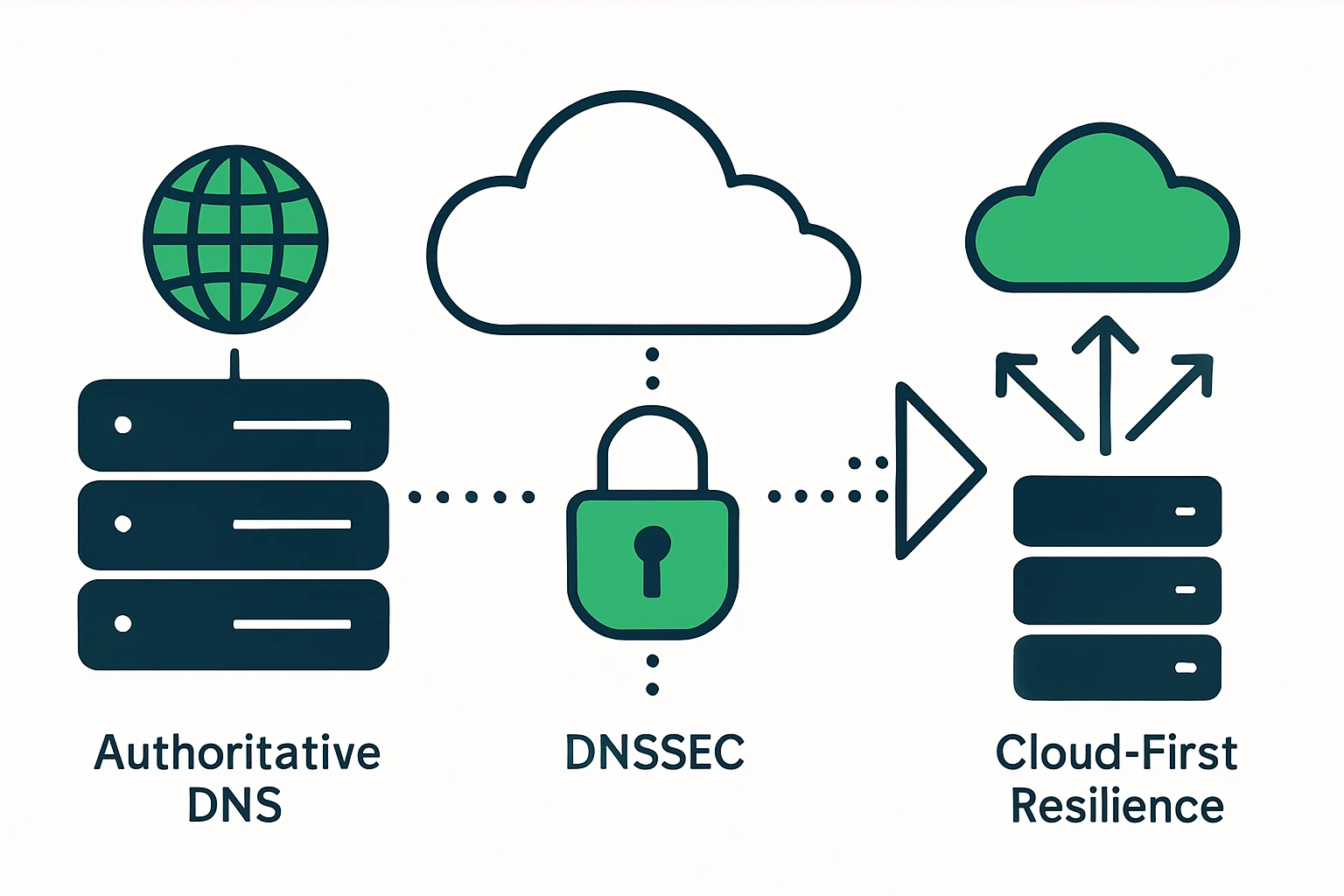
Successful enterprise DNS rests on four interconnected pillars: (1) authoritative DNS setup and zone architecture, (2) robust DNSSEC implementation, (3) deployment of Anycast for global resilience, and (4) cloud-native DNS architecture that harmonizes multi-cloud providers. Each pillar addresses distinct risk domains - availability, integrity, latency, and governance - and they must be designed to work together rather than in isolation. Google Cloud outlines the importance of an active-active, cross-provider approach to ensure DNS remains reachable even in the face of regional outages. (cloud.google.com)
Authoritative DNS setup: correct delegation and zone design
Authoritative DNS servers are the ultimate source of truth for a domain. A well-governed authoritative setup relies on properly configured zones, secure zone transfers, and clean delegation from parent zones to child zones. In practice, enterprises often distribute authoritative load across multiple data centers and cloud regions to minimize single points of failure while maintaining predictable delegation hierarchies. The core benefit is fast, accurate resolution for end users and services, with clear ownership of zone data and change control. For readers seeking a comprehensive view of how authoritative DNS underpins reliable name resolution, standard references describe the delegation model and the role of zone data in the DNS hierarchy. ICANN and IETF discussions provide a backdrop for best practices in DNS security and deployment. ICANN emphasizes the importance of secure, authenticated DNS infrastructure as part of the wider DNS ecosystem. (icann.org)
DNSSEC implementation: cryptographic validation at scale
DNSSEC adds cryptographic signatures to DNS data, enabling resolvers to validate that responses have not been tampered with in transit. The DNSSEC family of standards was developed through IETF efforts (with RFCs such as 4033, 4034, and 4035 forming the foundation) and has since become a global deployment priority in order to secure the DNS lookup process. ICANN has highlighted that DNSSEC deployment has progressed to broad adoption across generic top-level domains, underscoring its role as a foundational security layer for the DNS. A concise, practitioner-friendly overview from ICANN explains the core rationale and mechanism of DNSSEC, while ICANN’s deployment announcements confirm that DNSSEC is now deployed across all current gTLDs. For enterprise readers, anchoring your DNS with DNSSEC helps reduce risk from cache poisoning and man-in-the-middle-style tampering of DNS responses. ICANN: DNSSEC – What Is It and Why Is It Important? (icann.org)
Anycast deployment: resiliency and performance at scale
Anycast DNS distributes responses from multiple geographically dispersed servers, enabling the network to respond from the nearest or most optimal node. This approach typically yields lower latency and greater resilience against localized outages or traffic bursts. It also complicates DDoS attacks for the attacker, because a single target is not easily isolated to a single data center. For a practical, vendor-agnostic explanation of how Anycast improves speed and reliability, Cloudflare summarizes the concept and its security advantages, noting that Anycast setups are inherently more resilient to floods and outages than traditional single-point deployments. Cloudflare: What Is Anycast DNS? (cloudflare.com)
Cloud-native DNS architecture: multi-provider resilience
Designing a cloud-native DNS stack often means orchestrating across several cloud providers to avoid vendor lock-in and to gain cross-region fault tolerance. A practical, multi-provider perspective is described by Google Cloud in the context of hybrid and multi-provider DNS strategies, where DNS can be used in an active-active configuration to maximize availability and performance. The guidance emphasizes interoperability among providers (for example, using DNS forwarding and peering to connect on-premises and cloud environments) and the value of distribution across multiple providers to meet stringent service levels. Google Cloud architecture: Design considerations for hybrid multi-cloud (cloud.google.com)
A practical blueprint: multi-cloud, secure, and observable DNS
To operate at scale, enterprises benefit from a straightforward, repeatable blueprint that covers authority, security, resilience, and governance. The framework below translates these ideas into concrete actions for a real-world enterprise DNS program. It is deliberately agnostic about specific vendors to keep it usable across Route 53, Google Cloud DNS, Azure DNS, and other providers, while still aligning with the core concepts described by major cloud and DNS operators. The framework also helps bridge to the client resources listed later in this article.
- 1) Define authority and delegation – Establish clear ownership of each zone, publish authoritative NS records, and secure zone transfers between domains and their parent zones. Maintain an auditable change-control process for all DNS data changes.
- 2) Implement robust DNSSEC – Enable signing for zones where appropriate, publish DS records at parent zones, and ensure resolvers in the enterprise are configured to validate DNSSEC signatures. This protects end users from spoofed responses and improves trust in the DNS resolution chain.
- 3) Deploy Anycast and edge resilience – Distribute authoritative responses across multiple geographically dispersed nodes to minimize latency and survive regional disruptions. Align Anycast with your cloud regions and on-premise points of presence for consistent performance.
- 4) Build cloud-native, multi-provider DNS – Use active-active configurations across public DNS services to achieve higher availability and service levels. Integrate DNS deployment with multi-cloud strategies to avoid single-vendor risk and to support regulatory and governance requirements. Example in practice: enterprises often coordinate DNS across providers to maintain resolution continuity during provider outages and to optimize route efficiency for global endpoints. Google Cloud best practices provide concrete guidance for multi-provider DNS deployments in real-world environments. (cloud.google.com)
DNS monitoring, logging, and governance
Operational visibility is critical for uptime, security, and compliance. A mature enterprise DNS program should include continuous monitoring, centralized logging, anomaly detection, and auditable reports that align with commonly accepted governance frameworks. While the exact tooling varies by provider, the underlying objectives remain the same: detect unusual query patterns, track zone changes and transfers, and verify that DNSSEC validation is functioning as intended. Large-scale operators leverage end-to-end telemetry across on-prem and cloud deployments to enable rapid incident response and post-incident analysis.
For organizations pursuing formal assurance, SOC 2 and ISO 27001-type controls often shape the way DNS data is logged, stored, and accessed. Leading DNS providers publish their compliance posture to help customers assess risk and vendor fit. As part of due diligence, look for documentation and attestations that cover security, availability, and confidentiality of DNS data, as well as the controls around change management and incident response. For context on DNSSEC deployment and governance, ICANN notes the progress toward widespread DNSSEC adoption across gTLDs, underscoring the security rationale for managed, auditable DNS operations. ICANN: DNSSEC – What Is It and Why Is It Important? (icann.org)
Limitations, trade-offs, and common mistakes
Even well-designed DNS programs have limitations and potential missteps. Below are frequent challenges and how to mitigate them:
- Over-reliance on a single provider – While a single provider can be reliable, it introduces supplier risk. A multi-provider strategy improves resilience, but requires careful synchronization of zone data, DNSSEC keys, and policy enforcement across platforms. The multi-provider approach is explicitly discussed in modern cloud architectures as a way to increase uptime and escape vendor lock-in. Google Cloud best practices. (cloud.google.com)
- Misconfiguring DNSSEC – DNSSEC is powerful but adds operational complexity. Improper key management, DS record publication errors, or validation misconfigurations can break resolution for legitimate users. ICANN’s DNSSEC deployment materials and explanations emphasize correct adoption and ongoing validation practices. ICANN: DNSSEC overview. (icann.org)
- Inadequate observability – Without centralized logging and cross-provider telemetry, incident response slows dramatically. Aligning logging with governance requirements (e.g., SOC 2/ISO 27001 expectations) helps mature an organization’s security posture, even if the provider landscape changes. See general guidance from leading DNS practitioners on governance and compliance considerations.
Structured framework for practical implementation
Below is a compact framework you can apply when planning an enterprise DNS program. It is designed to be action-oriented, vendor-agnostic, and adaptable to Route 53, Google Cloud DNS, Azure DNS, and other providers.
- Frame: Four-layer DNS resilience
- Layer 1 - Authority and delegation: define zones, owner teams, and transfer controls.
- Layer 2 - Security: enable DNSSEC where appropriate, maintain key hygiene, and publish DS records.
- Layer 3 - Resilience: implement Anycast across multiple regions and providers, with explicit failover criteria.
- Layer 4 - Observability and governance: establish centralized logging, alerting, and periodic audits aligned to SOC 2 ISO controls.
Real-world integration: how this translates to practice
Many enterprises begin by cataloging domains under management and mapping them to their authoritative DNS deployment. As part of governance, they connect DNS inventory with security and compliance workflows so that changes in DNS data propagate through change-management pipelines and incident-response playbooks. For teams looking to augment their DNS inventories with vendor-friendly resources, Webatla offers domain directories that can be useful for asset discovery and compliance scoping. For example, Webatla’s .buzz domain directory provides a concrete listing that teams can reference during audits or migration planning. A broader index of domains by TLD is available at Webatla’s list of domains by TLD. Note: these resources are external to DNS Enterprises and are provided here for illustrative purposes of asset discovery and domain inventory workflows.
Limitations and common mistakes (revisited)
To close, remember that even a strong DNS program can underperform if governance and operational alignment are weak. Re-check your architecture against these critical questions: - Are zone transfers tightly controlled and auditable across all authoritative servers? - Is DNSSEC deployed consistently where it adds value, and are DS records correctly published at the parent zone? - Do you have a cross-provider Anycast strategy that matches your global user base and service endpoints? - Is your DNS data, changes, and logs integrated into a governance program that supports SOC 2/ISO-aligned controls?
Conclusion: a pragmatic, resilient DNS posture for modern enterprises
In an era of rapid cloud adoption and rising cyber risk, enterprise DNS must be purpose-built for reliability, integrity, and governance. An architecture that emphasizes authoritative setup, DNSSEC, and Anycast, implemented across multiple cloud providers, offers a practical path to improved uptime and security without sacrificing agility. The framework outlined here is intentionally modular so you can tailor it to your organization’s risk tolerance, regulatory requirements, and operational maturity. As you mature, you will likely need to extend your approach with richer telemetry, more formal compliance attestations, and continuous improvement cycles - while keeping DNS as a dependable, invisible backbone of your business operations. For teams exploring asset discovery in conjunction with DNS strategy, consider consulting public-domain resources and vendor documentation as a complement to your internal playbooks and controls.