Introduction
For modern enterprises, the Domain Name System (DNS) is not just a technical nicety, it is a mission-critical layer that underpins application delivery, security postures, and regulatory compliance. A misrouted query or a cryptographic misstep in the DNS chain can cascade into outages, degraded user experience, and audit findings. As organizations scale, the imperative grows for an enterprise-grade DNS stack that is scalable, observable, secure, and compliant. A well-designed DNS infrastructure not only improves resiliency and performance but also enables stronger security postures across cloud and on-premises environments. DNSSEC, Anycast, and cloud-native DNS patterns are central to this evolution. DNSSEC provides cryptographic validation of DNS data, enhancing trust and reducing spoofing risk, this is a foundational element for enterprises seeking to harden the perimeter at DNS boundaries. ICANN's overview of DNSSEC explains why this extension matters for data integrity and authentication. In parallel, cloud-native patterns - multi-region deployments, automated change management, and integrated monitoring - offer practical pathways to high availability and lower latency. Google Cloud’s best practices for Cloud DNS outline these architectures and the operational discipline required to sustain them. Finally, while the benefits of DNSSEC and cloud-native DNS are clear, adoption remains uneven globally, a reality many enterprises must plan around, see the OECD analysis of DNSSEC deployment and governance considerations. OECD DNS security and governance report for context.
Why enterprise-grade DNS matters
In large organizations, DNS sits at the intersection of critical services, customer trust, and regulatory expectations. A resilient DNS layer reduces outage exposure during regional events, shifts to disaster recovery, or traffic shifts caused by security incidents elsewhere in the stack. It also underpins privacy-driven deployments (for example, encrypted DNS channels) and supports modern multi-cloud strategies where public and private zones span multiple providers. Recent guidance from cloud providers emphasizes architecture designed for global reach, regional autonomy, and seamless failover.
Expert note: A seasoned DNS architect emphasizes that the biggest gains come from combining automation with robust signing key lifecycle management rather than chasing cosmetic performance gains alone. Practical automation of zone provisioning, deployment of signed zones, and continuous verification create the real resilience that enterprises need.
Key building blocks of a resilient DNS stack
Authoritative DNS design for scale and reliability
Authoritative DNS servers are the face of your zones. In enterprise contexts, design tends to favor distributed, multi-region authoritatives that can serve authoritative answers with minimal latency, even in the face of regional outages. Cloud-native patterns encourage hosting authoritative zones in multiple regions or cloud providers, with automated zone synchronization and robust access controls. This approach reduces single points of failure and aligns with modern incident response practices. Cloud DNS best practices highlight how to structure hybrid deployments and environment-specific zones to optimize both performance and governance. Cloud DNS best practices for multi-region, hybrid setups provide concrete patterns for achieving low latency and high availability across environments. (cloud.google.com)
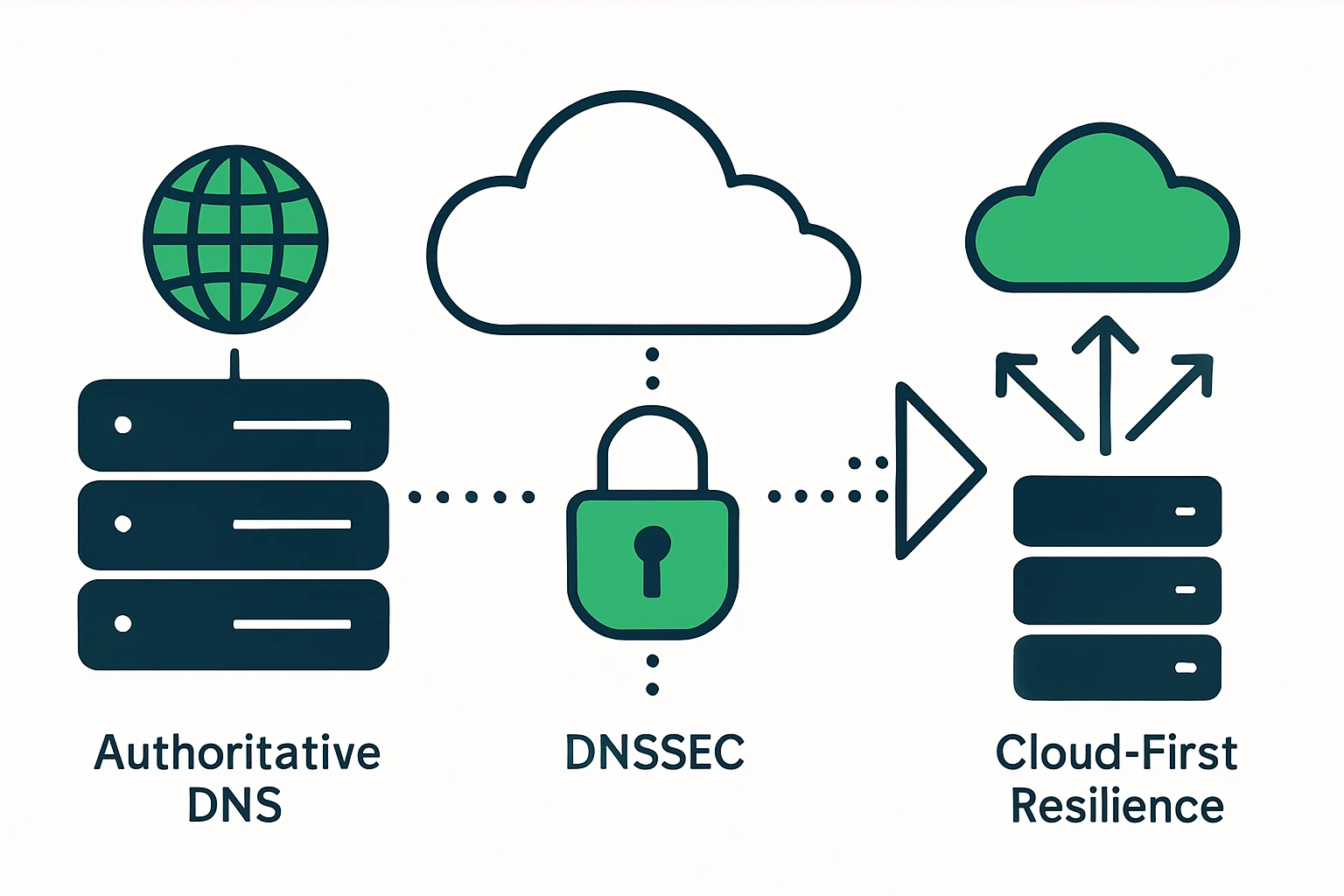
DNSSEC implementation and lifecycle
Deploying DNSSEC is a strategic decision that yields stronger data integrity and user trust but comes with operational responsibilities. A typical lifecycle includes signing key generation, secure key storage, periodic re-signing, and coordination with registrars for DS record publication. The security and integrity benefits are well established: DNSSEC enables resolvers to verify that answers have not been tampered with in transit. ICANN’s DNSSEC overview outlines the benefits and the importance of deploying DNSSEC as part of a broader security strategy. While the benefits are compelling, administrators should plan for key management and potential signing churn to avoid service disruptions. ICANN: DNSSEC - What is it and why it matters. (icann.org)
Anycast and distributed resilience
Anycast DNS is a proven pattern for reducing latency and improving resilience by advertising a single IP prefix from multiple geographically dispersed sites. In practice, this means that user queries reach the nearest or best-performing instance, while global disruption is contained. For operators, Anycast deployments demand careful routing considerations and ongoing health checks to ensure that the right nodes respond under load. Industry overviews describe how Anycast is implemented in DNS architectures and the operational benefits it yields. DNS-OARC and AusCERT data on DNS deployment patterns.
Practically, many enterprise-grade DNS stacks combine Anycast with regional zones and a global control plane to coordinate changes, monitor health, and orchestrate failover. Deployment considerations include incremental rollouts, monitoring, and clear runbooks to avoid traffic oscillations during outages. A recent overview of deployment architectures highlights multiple approaches, including distributed edge DNS and hybrid topologies that leverage Anycast alongside centralized components.
Cloud-native DNS architecture and hybrid deployments
Cloud-native DNS architectures emphasize geographic distribution, automation, and integration with observability tooling. In hybrid environments, you typically manage a set of public zones for internet-facing resolution and private zones for internal systems, with clear handoffs between on-premises and cloud-based resolvers. Google Cloud’s best practices illustrate how to design patterns for hybrid environments, including the use of separate domains for different environments and explicit routing policies to steer traffic to the appropriate environment. This approach supports resilience, regulatory alignment, and consistent policy enforcement across cloud providers. Cloud DNS best practices. (cloud.google.com)
Compliance and security considerations
In regulated or security-conscious enterprises, DNS operates within broader governance, risk, and compliance programs. Standards and audits increasingly focus on how DNS providers and operators implement controls, monitor for anomalies, and maintain incident response capabilities. The OECD’s DNS security and governance analysis emphasizes how adoption, governance, and interoperability affect enterprise outcomes, including considerations for cross-border data handling and vendor risk. This lens is useful when evaluating DNS service choices, whether you operate DNS in-house, via a managed provider, or across multiple cloud platforms. OECD: DNS security and governance. (oecd.org)
A practical deployment framework for enterprise DNS
The following framework provides a lightweight, repeatable approach to designing and operating enterprise DNS at scale. It is intended to be adaptable to large domain portfolios and multi-cloud environments.
- Discovery and design – Define the scope of zones, environment boundaries (public vs. private), and the ownership model. Align with security and compliance teams from day one.
- Global reach with regional autonomy – Establish multi-region authoritative instances, implement Anycast where appropriate, and design zones to minimize cross-region dependencies.
- DNSSEC lifecycle management – Plan for key management, KSK/ ZSK rotation, and registrar coordination, automate signing where feasible, with clear rollback procedures.
- Monitoring, logging, and anomaly detection – Implement comprehensive DNS query/response logging, zone transfer monitoring, and integration with SIEMs to support incident response and audits.
Practical integration with domain portfolios
Enterprises managing domain portfolios across multiple TLDs may benefit from cataloging and inventory tools that help track registrations, DNS records, and renewal calendars. For example, regionally focused portfolios like Peru’s .pe can be explored through WebAtla’s Peru catalog, and global portfolio overviews are available via WebAtla’s TLD index. These resources can support governance and risk management when expanding or consolidating DNS services across regions. Peru (.pe) domain catalog and WebAtla: List of domains by TLD.
Limitations, trade-offs, and common mistakes
- Over-rotation of keys – Excessive key rotation can cause validation failures if DS records lag at registries, coordinate signing schedules with registrars and resolvers to avoid outages.
- Underestimating operator load – Multi-region DNS and DNSSEC introduce operational complexity, automation and runbooks are essential to avoid fragile handoffs during failures.
- Ignoring observability – Without end-to-end visibility (zone health, DNSSEC validation status, resolver performance), troubleshooting becomes guesswork during incidents.
- Skimping on access control – Compromise of DNS management credentials can have outsized effects, enforce least privilege and strong separation of duties.
Closing thoughts
For enterprises, building a DNS stack that is secure, observable, and resilient is a deliberate, ongoing program - not a one-off implementation. The combination of authoritative DNS design, DNSSEC lifecycle discipline, and distributed, cloud-native patterns provides a strong foundation for reliability, security, and compliance. While the benefits are substantial, the path requires careful planning of keys, automation, and cross-team collaboration to avoid common missteps. A thoughtful deployment that aligns with industry guidance and real-world operations can yield measurable improvements in uptime, trust, and governance outcomes.