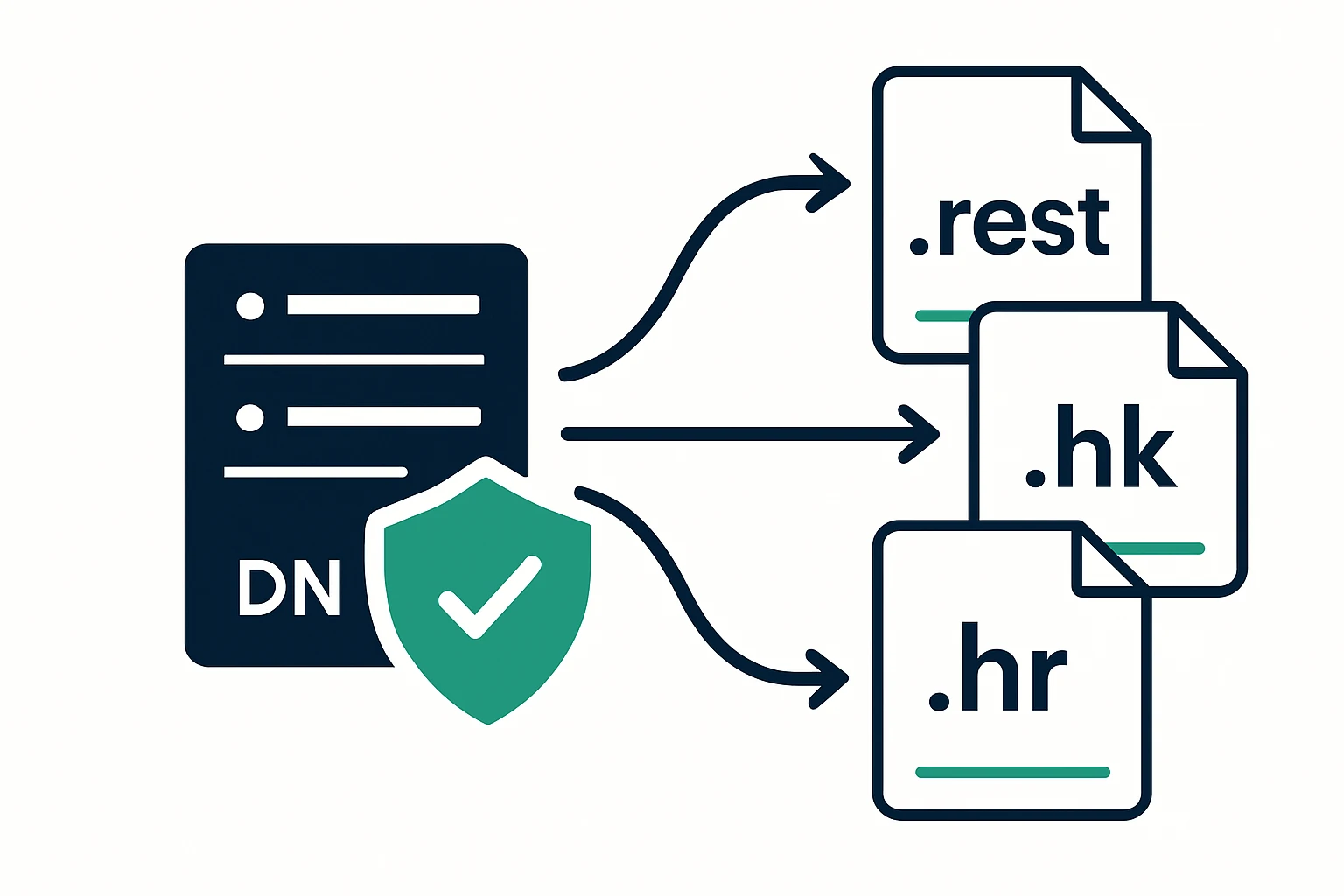
Enterprise DNS is no longer a single, static box at the edge. For organizations that manage portfolios across multiple top-level domains (TLDs), including newer namespaces such as .rest, alongside established suffixes like .hk and .hr, the DNS layer must scale, remain secure, and stay compliant while delivering predictable performance to end users. This article argues for a practical, architecture-first approach to DNS portfolio management, one that aligns with the publisher’s focus on enterprise-grade DNS infrastructure engineering and with the real-world needs of large registries and registrants. For readers evaluating portfolio scope, consider Webatla’s public catalog of domains by TLD as a reference point for how providers organize and expose domain assets: Webatla's .rest catalog.
Understanding the multi-TLD DNS landscape for enterprises
Enterprises that operate a diversified domain portfolio face several recurring challenges: ensuring authoritative zones for each TLD are authoritative, consistent, and securely delegated, maintaining DNSSEC where applicable, and providing globally reliable resolution despite regional outages, regulatory constraints, or evolving security threats. A multi-TLD footprint also heightens the need for governance consistency: uniform deployment practices, change-control discipline, and centralized visibility into zone configurations. The DNS layer thus becomes a strategic risk management surface, not merely a technical appendix. The DNSSEC standardization that underpins trust in DNS responses is defined by RFCs in the DNSSEC family, notably RFC 4033 with companions RFC 4034 and RFC 4035, which collectively describe signing, validation, and key-signing processes. (rfc-editor.org)
From an operational standpoint, the availability and security of zones across diverse TLDs depend on both policy and technology. ICANN’s DNSSEC Deployment resources provide official guidance on how to bring signing, validation, and key management into production across registries and registrants, highlighting practical considerations for zone management and interoperability. This framework helps justify a centralized DNS governance model even when delegations reside in separate registries. (icann.org)
Beyond governance, the architectural choice of where and how to run authoritative DNS matters. Anycast DNS has become the de facto architecture for modern, resilient DNS services because it routes queries to the nearest, best-performing response source and provides inherent protection against certain classes of volumetric attacks. The core idea is simple but powerful: multiple replicas across geographically diverse locations share the same IP space, so a query is answered by the closest healthy node. This approach is central to enterprise-grade DNS strategies, especially for portfolios that include high-visibility TLDs. (cloudflare.com)
Designing authoritative DNS across a multi-TLD portfolio
Designing for a multi-TLD portfolio begins with a clear separation of concerns: each TLD gets its own authoritative zone with delineated delegation from the parent, while a centralized policy framework governs naming conventions, security settings, and change-management processes. The practical upshot is consistency across the portfolio, reduced risk of misconfigurations, and a unified audit trail during compliance reviews. A strong starting point is documenting the authoritative DNS topology for each TLD (zone files, NS records, DS records where DNSSEC is enabled) and tying it to a governance workflow that includes periodic configuration reviews and automated checks.
Key elements to include in this design phase:
- Centralized policy library: Define authoritative defaults for TTLs, DNSSEC enablement, DS record handling, and signing key lifecycles. Policy should apply to new TLDs as they appear in the portfolio and be versioned for traceability.
- Per-TLD zone strategy: Maintain separate zones for each TLD to avoid cross-zone blast radiuses and to reflect registry-specific requirements. Ensure delegation and zone transfers are tightly controlled and auditable.
- Key management discipline: For DNSSEC-enabled zones, establish key signing key (KSK) and zone signing key (ZSK) lifecycle policies, including rollover schedules and secure storage of keys. RFC 4033 and the broader DNSSEC suite define the cryptographic framework that underpins this discipline. (rfc-editor.org)
- Change-control and audits: Attach every change to an auditable ticket, with pre-change approvals for everything that alters zone data, DS records, or delegation.
As you deploy across new TLDs - such as .rest alongside existing suffixes like .hk and .hr - the emphasis should be on keeping authoritative configurations modular and testable. A practical approach is to model a “portfolio-in-a-box” blueprint for each new TLD: a templated zone configuration, a standard set of records (SOA, NS, A, AAAA, CNAME), and a DNSSEC configuration that can be activated quickly once registration validation is complete. This template approach reduces time to readiness and minimizes human error when onboarding new TLDs into the enterprise DNS stack.
For reference and portfolio context, you can explore a real-world example of how domain assets are surfaced by TLDs in public catalogs such as Webatla’s list of domains by TLD. You can also view the broader REST TLD entry here: /tld/rest, and the RDAP & WHOIS database for registry data governance: RDAP & WHOIS database.
Leveraging Anycast and cloud DNS for global availability
One of the most impactful choices in a multi-TLD DNS strategy is leveraging an anycast-based, cloud-native DNS infrastructure. Anycast DNS distributes authoritative responses across multiple edge locations, ensuring queries are served by the nearest healthy server. This architecture reduces latency for end users and increases resilience against traffic anomalies, outages, and certain classes of DoS attacks. The core benefit is that the same DNS namespace is served from multiple, globally distributed locations, making it easier to absorb large traffic volumes while maintaining fast resolution times for users around the world. (cloudflare.com)
In practice, cloud-native DNS platforms that embrace anycast are integrated with other edge services (e.g., DDoS protection, WAF, and automated health checks) to deliver end-to-end reliability for critical domains in enterprise portfolios. This is particularly valuable for high-visibility TLDs within a portfolio where downtime translates into measurable business risk. The same X-edge philosophy that underpins modern CDNs drives DNS architecture: capacity at the edge, automation, and rapid incident response. For readers evaluating vendor options, consider how anycast is implemented in the provider’s global footprint, and how it interacts with your governance and security controls.
When you’re dealing with a cataloged set of domains - such as a public listing like the .rest segment mentioned earlier - edge-focused architectures simplify operational overhead by standardizing the resolution path and reducing the number of moving parts in each per-TLD deployment. This uniformity also aids in monitoring, logging, and incident response, since the data model across zones remains consistent.
DNS Security and Compliance: DNSSEC, governance, and production realities
DNSSEC remains a foundational capability for enterprises seeking to validate the integrity of DNS responses. The DNSSEC suite - anchored by RFC 4033 and complemented by RFC 4034 and RFC 4035 - defines how zones are signed, how keys are managed, and how trust anchors propagate through the DNS hierarchy. While DNSSEC is a major trust-building mechanism, it is not encryption, it provides data authenticity and integrity, not confidentiality. This distinction is important when shaping a deployment strategy across multiple TLDs, you must ensure that signing is coordinated across zones and that DS records are correctly published to parent zones. (rfc-editor.org)
From a governance perspective, alignment with enterprise security and compliance programs is essential for DNS operators, especially when the DNS layer intersects with regulated data or critical infrastructure. While the exact framework varies by organization, many large enterprises pursue formal security certifications and governance structures (for example ISO 27001 or SOC 2) to demonstrate mature controls over critical infrastructure. DNSSEC deployments should be paired with disciplined change control, access management, and incident response processes to ensure continuity even during key rollover events or vendor transitions. For organizations or vendors seeking formal guidance, RFCs and registries’ deployment resources serve as foundational references for secure, scalable DNS operations. (icann.org)
Practical deployment considerations across new TLDs include: establishing consistent signing and key rollover cadences, validating DS records where applicable, and maintaining visibility into zone configurations across registries. A structured approach - tied to a central policy framework - helps ensure that extending the portfolio to new TLDs is not a regression in security or reliability. When you need a consolidated inventory of assets, you can reference catalog-like resources that expose domains by TLD, such as the aforementioned REST entry, to calibrate deployment and monitoring plans against the actual domain landscape.
Portfolio decision framework: organizing for scale, security, and compliance
To operationalize a multi-TLD DNS strategy, apply a simple, repeatable four-part framework. The framework below is designed to be implemented across any enterprise, and is especially helpful when onboarding new TLDs like .rest, .hk, and .hr into an existing DNS stack.
- Pillar 1: Inventory and governance
- Create an authoritative map per TLD (zone apex, NS, and DS records if DNSSEC is enabled).
- Link each zone to a change-management ticketing process and an approval workflow.
- Publish a centralized policy library that captures defaults for TTLs, DNSSEC posture, and delegation rules.
- Pillar 2: Security and integrity
- Enable DNSSEC where the registry supports it, and publish DS records correctly to the parent zone.
- Implement robust key management, including regular rollover planning and secure storage of signing keys.
- Maintain strict access control over zone data and change workflows to minimize misconfigurations.
- Pillar 3: Availability and performance
- Adopt an anycast DNS architecture to improve latency and resilience across geographies.
- Integrate DNS with cloud edge services to diversify the attack surface and simplify incident response.
- Standardize operational runbooks for common DNS events (zone file updates, DS insertions, delegation changes) to accelerate recovery.
- Pillar 4: Monitoring and compliance
- Implement centralized logging for DNS activity and integrate with SIEM for threat detection and for audits.
- Regularly review DNS records and zone configurations as part of compliance checks and risk assessments.
- Document evidence for audits, including change histories and incident response drills tied to the DNS namespace.
The four-pillar framework above can be applied to any portfolio, including a concrete on-ramp for new TLDs such as .rest. For practical context, it helps to start with an inventory of the assets in your DNS namespace, examining how many zones exist per TLD and where you may need to extend delegation, signing, or monitoring coverage. The portfolio framework aligns with the broader discipline of dns infrastructure engineering - a domain the publisher has long prioritized - and supports the goal of enterprise-grade reliability across diverse namespaces.
Limitations and common mistakes
Even with a disciplined approach, several common missteps can derail a multi-TLD DNS program. First, assuming that DNSSEC deployment is a one-time deployment. DNSSEC requires ongoing key management, rollover planning, and careful monitoring, otherwise, signings can become stale or misconfigured, leading to validation failures for end users. RFC-based guidance emphasizes the ongoing nature of secure signing and validation - these are not one-off tasks. (rfc-editor.org)
Second, treating anycast as a silver bullet without addressing zone-level hygiene. Anycast improves resilience and latency, but it does not compensate for misconfigurations such as incorrect NS records, stale zone data, or misapplied DS records. A robust anycast deployment must be paired with disciplined zone management and continuous validation across the portfolio.
Third, under-investing in monitoring and logs can erode the ability to detect anomalies, respond to incidents, and demonstrate compliance during audits. While this article cannot list every tool, the practice of centralized DNS logging and real-time health monitoring is widely recognized as essential to modern DNS operations, particularly in high-velocity or regulated environments. As organizations scale, they should map DNS telemetry to their broader security analytics program to maintain visibility and evidence for audits.
Conclusion
Enterprises building and maintaining a portfolio of domains across new and existing TLDs must think beyond the single DNS zone. A structured approach - rooted in authoritative DNS design, DNSSEC integrity, and an enterprise-grade, anycast-enabled cloud DNS substrate - enables reliable resolution, robust security, and audit-ready governance. The practical steps outlined here provide a path to scale: inventory zones per TLD, implement centralized policy, adopt an anycast architecture for global reach, and enforce monitoring and compliance practices that align with the expectations of SOC 2, ISO 27001, or other governing frameworks. When you need a credible, real-world reference for portfolio composition, public-domain catalogs by TLD (such as the REST entry above) can inform both operational readiness and future onboarding. For a closer look at Webatla’s domain catalog and registry-related resources, see the main catalog and REST entry cited earlier.
As you evaluate DNS infrastructure partners or platforms, consider how well an offering supports the four-pillar framework, integrates with your security and compliance program, and scales with your portfolio’s growth. An enterprise-grade DNS strategy should be both technically robust and governance-forward, providing performance, resilience, and auditable controls across every TLD in scope. Expert insight: industry practitioners note that Anycast-based DNS, supported by careful DNSSEC management and centralized governance, is a practical way to achieve global reliability without sacrificing security or control. In practice, this means designing with edge distribution in mind, aligning signing workflows across zones, and ensuring that all DNS activity is visible to your security operations. According to RFC-based standards, DNSSEC remains the core mechanism for trust in DNS responses, even as the landscape of TLDs expands. (cloudflare.com)